Author’s Note (Updated September 2025):
Agile PLM has now logged 15 vulnerabilities since 2018* — six in the past year alone. Two of those, CVE-2024-21287 and CVE-2024-20953, are application-level flaws listed in CISA’s Known Exploited Vulnerabilities (KEV) catalog. With Premier Support winding down ahead of Agile’s December 2027 End of Life, the system is moving from “legacy” to liability.
Public sources like the National Vulnerability Database (NVD) and Oracle’s own Critical Patch Updates confirm these disclosures (see References below).
From Legacy System to Active Target
For years, Agile PLM was considered dependable — old, yes, but steady. That perception no longer holds. In just 12 months, six new vulnerabilities were disclosed. The two I’ll focus on (21287 and 20953) aren’t just technical defects — they’ve been exploited in the wild. Real businesses have experienced losing governance over their own IP.
Each disclosure is a reminder: attackers see Agile as a viable target. Each patch is a temporary reprieve, not a cure. Once Premier Support ends, new vulnerabilities will remain permanently unpatched.
Key Facts at a Glance
- CVE-2024-21287 (Nov 2024): High-severity (CVSS 7.5 out of a possible 10, by severity). Remote file extraction without authentication. Patched in RUP 28. KEV-listed.
- CVE-2024-20953 (Feb 2025): Critical (CVSS 9.9). Remote exploitation enabling full control. Patched in February 2025 Critical Patch Update (CPU). KEV-listed.
- Four additional framework-related CVEs disclosed Jan 2025: CVSS scores ranging from 6.5 to 9.9.
- CVEs since 2018: At least 15 publicly disclosed.

Cybersecurity and Infrastructure Security Agency (CISA), publisher of the Known Exploited Vulnerabilities (KEV) catalog.
The Escalating Pattern
Historically, most Agile CVEs (excluding third-party instances) are tied back to frameworks like WebLogic and Java. That was still worrying but manageable. What’s changed is the clustering:
- Two application-level KEV CVEs in three months.
- Four framework CVEs in a single CPU release.
- Six total CVEs in less than a year.
This isn’t random — it indicates that Agile PLM is drawing more scrutiny from the security community as its end-of-life approaches.
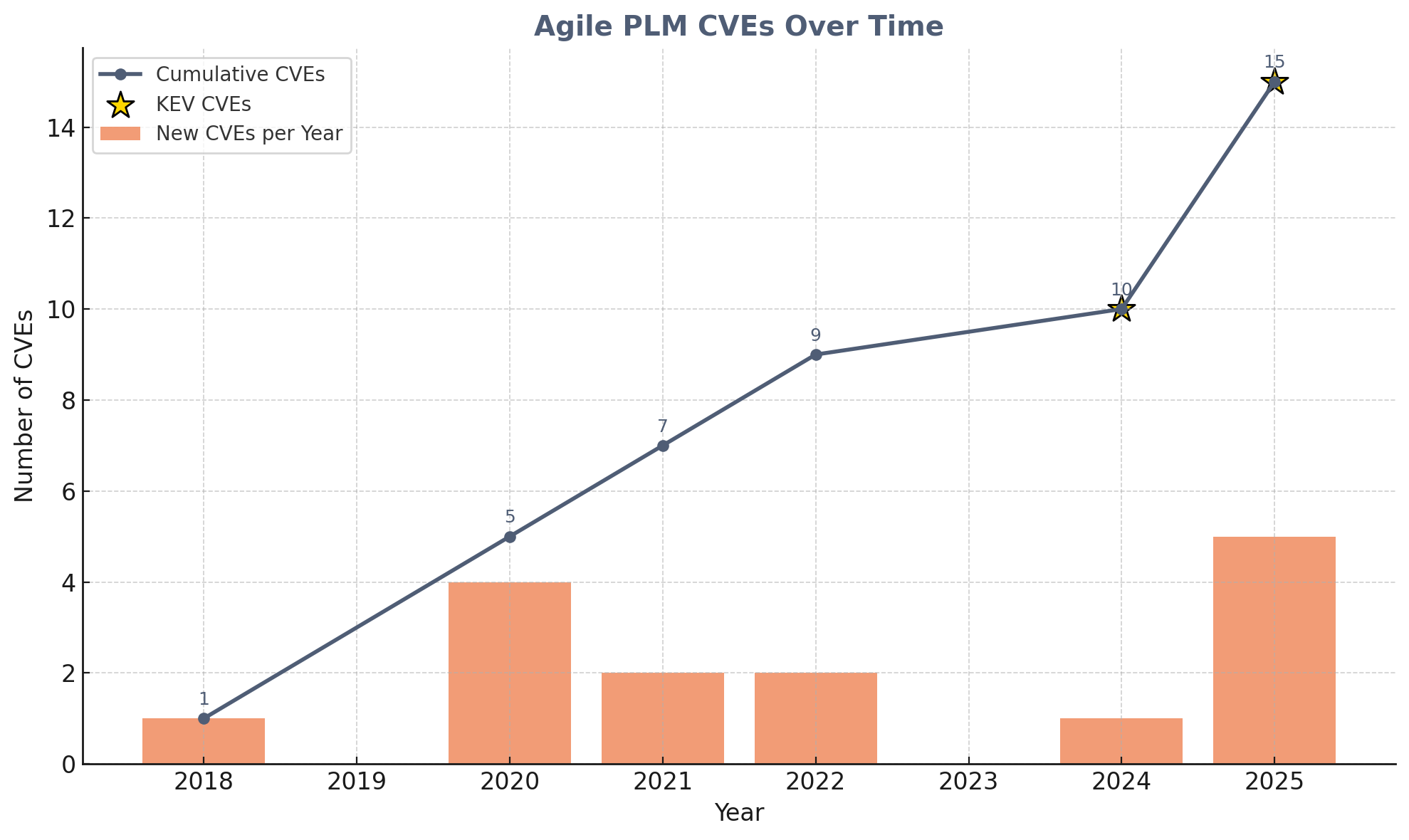
Agile PLM CVEs from 2018–2025. Orange bars show annual disclosures, the blue line tracks the cumulative total, and gold stars mark vulnerabilities later added to CISA’s Known Exploited Vulnerabilities (KEV) catalog. This chart includes CVEs documented in Oracle CPUs as impacting Agile PLM; broader WebLogic/Java framework CVEs are excluded for clarity.
What It Means for Agile Users
- Short-term: Quarterly patching, however irksome, remain essential. Apply Agile RUP 28 and all subsequent CPUs. Audit access controls. Monitor closely.
- Medium-term: Accept that patching is a stopgap. Premier Support ends in 2027; exposure only grows from there.
- Long-term: Begin migration planning now. Data cleansing, integration rebuilds, and user retraining take years, not months. Delaying leaves you competing for limited partner capacity.
See how Domain Systems handles complex data migrations.
What Smart Leaders Are Doing Now
“Security threats like this reinforce why we’ve been advising our clients to assess their long-term PLM strategy. It’s not just about fixing today’s problem; it’s about ensuring your IP remains protected for the future.”
— Randy Pettit, President, Domain Systems
Steps worth taking:
- Apply Oracle’s latest patches immediately. Schedule a patch installation.
- Commission a health check to understand your system’s risk profile.
- Treat migration not as a technical upgrade, but as a security initiative.
Final Call
Six vulnerabilities in less than a year — including two KEV-listed exploits show that Agile PLM continues to attract security attention as it nears its 2027 support end date.
Apply the patches.
Assess your exposure.
Build your roadmap now — before the window closes.
Sources
Note: Aggregator sites like cvedetails.com and vulmon.com vary in how they classify Oracle Agile PLM vs. its underlying frameworks (WebLogic, SDK, Integration Services). Figures were cross-checked against NVD and Oracle’s CPU advisories for accuracy.


Thanks for reading!
Do you think we’ve already seen the bulk of Agile PLM’s vulnerabilities disclosed? Or should teams expect a steady trickle right up until Premier Support ends in 2027?